IoT Applications in Image Processing
Machine vision is playing an increasingly important role in the Internet of Things. Various sensors and cameras provide a large amount of data and thus enable ever more diverse applications. Find out what the IoT is and the benefits of image processing.

What is the IoT?
In the Internet of Things, intelligent devices and machines are networked via the internet. Data can be collected at various points during processes, for example within a smart factory, and processes can be controlled and optimized - for example: using artificial intelligence. Sensors and cameras can be important elements for data collection and this data can be processed in real time using increasingly sophisticated technology.
Applications from the Internet of Things can be found in various areas, such as: consumer devices, medicine, agriculture, smart home, retail, Industry 4.0, and industrial IoT (IIoT for short) solutions.
Technological leap for your application
More and more sensors and cameras are now providing a large amount of data in a wide range of IoT and IIoT applications. Self-learning capability and modular long-term autonomy play a major role here.
IoT becomes smarter, more efficient, and more flexible with computer vision
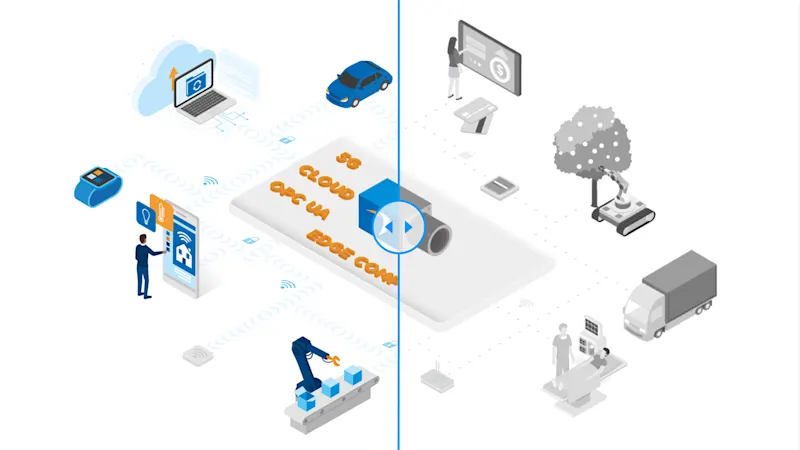
The efficient evaluation of the collected data in real time is crucial for the IoT: reducing latency times is made possible by edge computing and 5G technology. With industrial AI and new algorithms for machine learning, another major step toward even more efficient production, new business models, and applications is coming into focus.
AI is no longer science fiction, it is a real and essential part of the networked world and "Industry 4.0". Modern edge computing solutions enable data analysis to be relocated to the place where the data is collected. At the same time, data transmission is accelerated by 5G technology, reducing latency times and speeding up data exchange in real time. OPC UA is a standardized communication protocol for enabling this real-time communication between machines. Meanwhile, cloud solutions help make applications or machine learning models available - when storing data or even evaluating it.
IoT applications with image processing
AI-based "zero-defect production" is being driven forward in smart factories, and predictive maintenance is further reducing downtimes. IoT solutions in logistics processes are increasing efficiency and shortening delivery times. New home applications are further networking our private lives. Diagnostic possibilities in medical technology are increasing and the agricultural sector can also aim to reduce the use of resources while increasing automation.
Computer vision and IoT
Computer vision is becoming increasingly important for applications in the IoT of the future. Today, however, many image processing systems have not yet reached the standard that the IoT will need in the future.
IoT of the future
Reducing the amount of data through powerful edge computing
Energy efficiency through new technology
Fast image analysis through deep learning and/or AI, low latency thanks to 5G
Communication standard: OPC UA for computer vision
Improved security through more economical data exchange
IoT today
Limited bandwidth; "classic" image processing
High resource and energy requirements
Long latency times
No communication standard
Security gaps
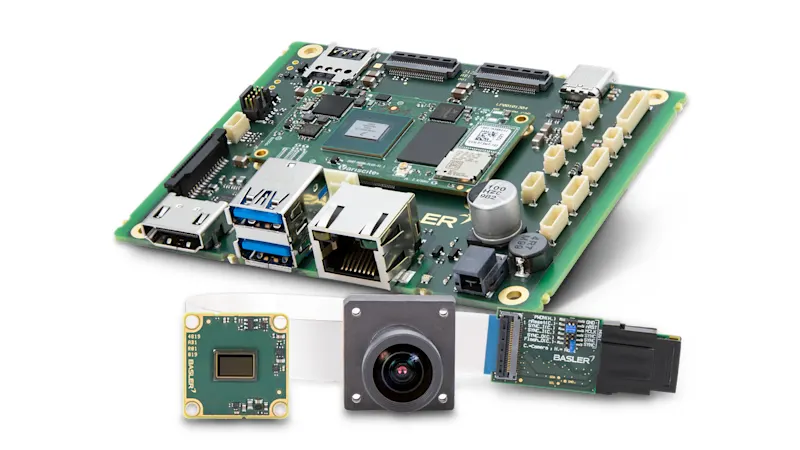
Our prototyping products for IoT solutions
Here you can find our prototyping products that easily integrate computer vision into IoT applications:
Background information on IoT and vision technology
Need more background information on IoT and vision technology? These articles may help: